The discovery of unconventional keywords—those unexpected, long-tail, or question-based phrases that reveal nuanced user intent—often feels like striking gold.They promise a path to less competitive, highly engaged audiences.
Essential Technical Foundations for Hosting Modern Digital Tools
The decision to host a digital tool—whether a sophisticated SaaS application, a collaborative workspace, or a custom internal platform—extends far beyond the initial purchase or development. Its success, security, and scalability are fundamentally rooted in the technical bedrock upon which it is deployed. Navigating the key technical considerations for hosting is not merely an IT formality; it is a strategic exercise that dictates performance, cost, and long-term viability. The primary pillars demanding rigorous assessment are infrastructure architecture, security and compliance, performance and scalability, and ongoing maintenance and monitoring.
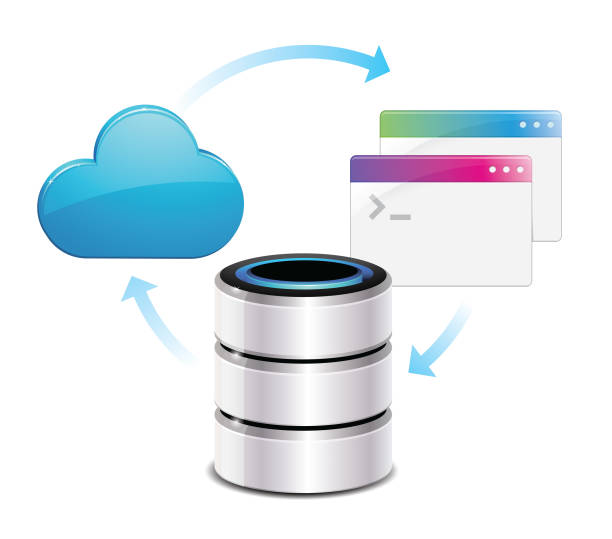
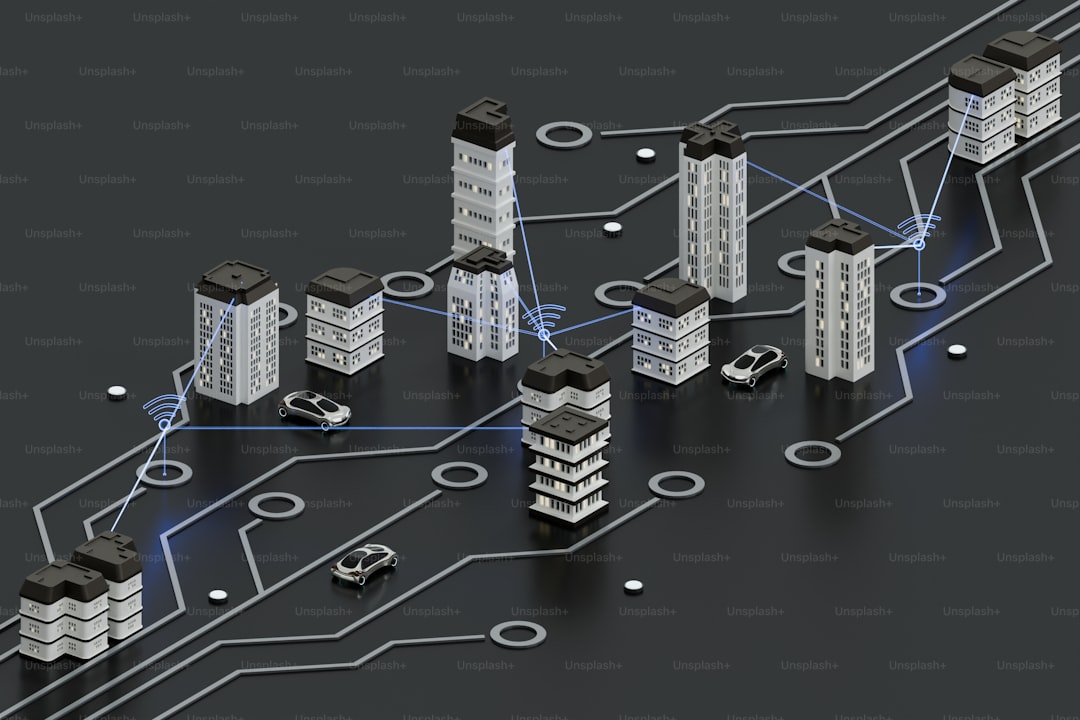
At the core lies the choice of infrastructure architecture, a decision that sets the trajectory for nearly every other consideration. The traditional model of physical, on-premises servers offers maximum control but demands significant capital expenditure and in-house expertise. Conversely, cloud-based solutions, leveraging providers like AWS, Azure, or Google Cloud, present a paradigm of elasticity and operational expenditure. Within the cloud, further architectural choices emerge, such as between monolithic applications and more agile, decoupled microservices. The selection here directly influences deployment agility, resilience, and the complexity of management. Furthermore, the architecture must account for data storage strategies, deciding between SQL databases for structured data and NoSQL alternatives for unstructured or rapidly scaling data, each with profound implications for query efficiency and future growth.
Intertwined with architecture is the non-negotiable domain of security and compliance. Hosting any tool necessitates a multi-layered defense strategy. This begins with robust network security, employing firewalls, intrusion detection systems, and secure network configurations to shield against external threats. Data encryption, both for data at rest within storage systems and in transit between the user and the servers, is equally critical. Equally important is access control, implementing the principle of least privilege through stringent authentication and authorization protocols. For tools handling sensitive user information, particularly in regulated industries like healthcare or finance, compliance with frameworks such as GDPR, HIPAA, or PCI-DSS is not optional. The hosting environment must provide the technical capabilities and audit trails necessary to demonstrate adherence, influencing everything from data locality rules to breach notification procedures.
The user experience is directly governed by performance and scalability considerations. Performance hinges on factors like server response times, which are influenced by computational power (CPU), memory (RAM), and the speed of underlying storage, such as SSDs. Strategic use of Content Delivery Networks (CDNs) can dramatically improve global access speeds by caching static assets geographically closer to end-users. Scalability, however, is about capacity planning for the future. A successful tool will attract more users and data, and the hosting solution must accommodate this growth seamlessly. Horizontal scalability, the ability to add more servers to a pool, is often favored in cloud environments for its flexibility over vertical scaling (upgrading a single server’s power). Effective hosting plans for these elements, ensuring the tool remains responsive during traffic spikes without incurring excessive costs during quieter periods.
Finally, the lifecycle of the hosted tool depends on diligent maintenance and monitoring. A proactive approach requires comprehensive monitoring systems that track server health, application performance, error rates, and security anomalies in real-time. Automated alerts allow teams to address issues before they impact users. Furthermore, a reliable backup and disaster recovery strategy is paramount; regular, tested backups and a clear recovery plan mitigate the risk of data loss from hardware failure, human error, or cyberattacks. The hosting model also dictates the operational burden: managed services can alleviate the load of patching, updates, and server maintenance, while unmanaged options offer control at the cost of dedicated internal resources.
In conclusion, hosting modern digital tools is a complex technical symphony, not a simple act of deployment. The interplay between a resilient and scalable infrastructure, an impregnable security posture, performance-optimized resources, and continuous operational oversight forms the essential foundation. Overlooking any of these interconnected considerations can lead to systemic failure, data catastrophe, or stifled growth. Therefore, a deliberate and informed approach to these technical fundamentals is not just about keeping the lights on; it is about building a secure, responsive, and adaptable platform that allows the tool—and the business it serves—to thrive now and in the future.